Google’s Willow Quantum Computer
Credit: Google Quantum AI
Quantum computers capable of breaking internet security codes are rapidly approaching reality. Discoveries from two research teams highlight the strides being made, indicating that current quantum machines are already over halfway to the necessary scale.
Both studies focus on cryptographic methods centered around the Elliptic Curve Discrete Logarithm Problem (ECDLP)—a mathematical challenge ideally suited for data encryption. ECDLP has been widely adopted for securing internet communications, including banking transactions and major cryptocurrencies like Bitcoin.
While classical computers struggle to breach elliptical curve-based codes, it has been understood since the 1990s that quantum computers possess the ability to do so. However, building a sufficiently powerful quantum computer seemed a far-off challenge due to engineering limits.
Recent advancements in both theory and engineering have drastically accelerated this timeline. Theoretical research has led to optimized quantum hacking algorithms, significantly lowering the required quantum computing power. For instance, in 2019, estimates indicated a need for 20 million qubits to crack a related encryption system called RSA-2048; by February, that figure plummeted to just 100,000 qubits.
Furthermore, while the most sophisticated quantum computers in 2019 barely exceeded 50 qubits, today’s leading machines have surpassed 1,000 qubits, with the largest unused qubit array containing 6,100 qubits.
Currently, Dorev Bruchstein and his team suggest that ECDLP could require machines with only 10,000 qubits. Though this decoding would still take years, Ryan Babush and his colleagues from Google’s Quantum Research division have shown that just 500,000 qubits could perform the task in as little as nine minutes.
“Today marks a significant moment for quantum computing and cryptography,” says Justin Drake of the Ethereum Foundation, which collaborates with researchers at Google. He shared this insight via social media.
Bruchstein’s estimates are based on qubits formed from ultracold atoms manipulated by lasers, providing increased connectivity that likely reduces the number of required qubits.
Bruchstein envisions a potential array of 10,000 ultracold qubits being realized within a year, yet controlling and operating them with precision will be a significant challenge. Proper interaction between qubits is critical, eliminating the possibility of merely linking multiple existing machines together.
Bruchstein anticipates that a fully operational quantum computer may not be available until the decade’s end. “We’re making substantial progress, but it’s beginning to feel feasible to build,” he explains.
Concerns Over Cryptocurrency Security
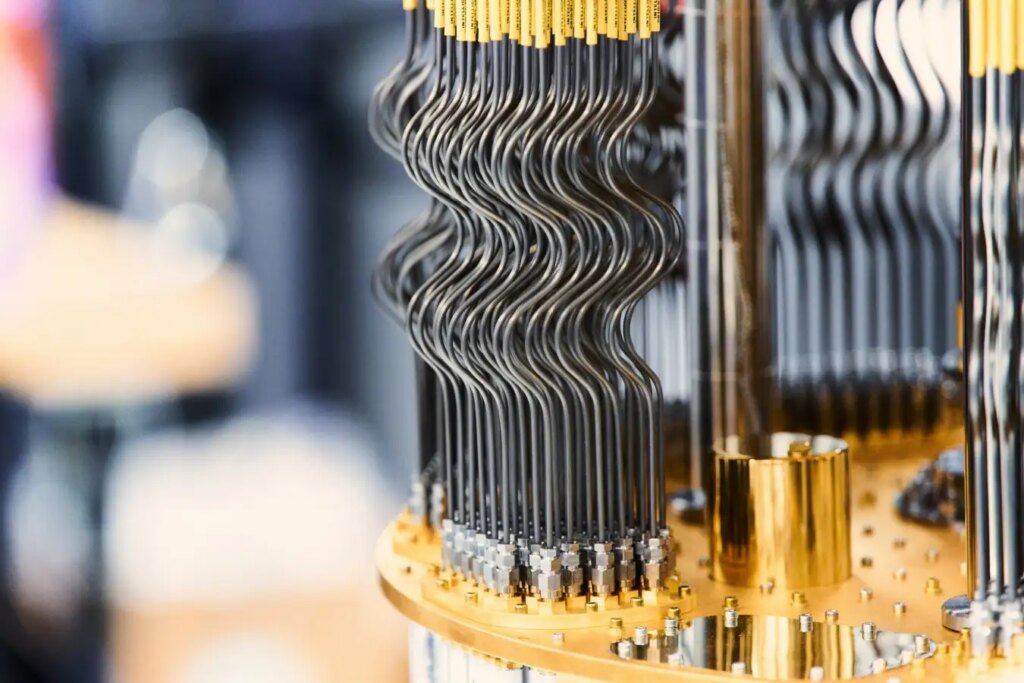
The Google team derived their conclusions based on a different type of quantum computer using superconducting circuits. These quantum systems are often viewed as more advanced, and Google prioritizes their development.
The researchers have refrained from commenting publicly about the study. However, the paper indicates that “resource estimations could be dramatically lowered with more aggressive hardware capabilities,” implying that the 500,000 qubit target might be conservative. Notably, they refrain from providing details about the decryption algorithm for security reasons.
They also indicate that such quantum computers could potentially intercept cryptocurrency transactions and reroute funds for a brief period before recording, effectively enabling theft.
Given the findings from both studies, it’s clear that Bitcoin may be more susceptible to quantum attacks sooner than previously understood, according to Scott Aaronson from the University of Texas at Austin.
Stefano Gozioso from the University of Oxford notes that both configurations of quantum computers encounter substantial engineering hurdles before practical application is achievable, particularly the ultracold atom method, which is still largely experimental. He emphasizes the growing urgency for security in the digital realm.
Some internet browsers already implement encryption impervious to quantum attacks, termed post-quantum cryptography (PQC). While traditional banking systems may adapt post-attack, a decentralized cryptocurrency framework might be far more vulnerable, according to Gozioso. Google suggests that organizations transition to PQC by 2029 as the need intensifies.
“This is precisely why we initiated the PQC standardization project over a decade ago,” states Dustin Moody from the National Institute of Standards and Technology (NIST). “We anticipated that advancements in quantum hardware would coincide with algorithmic progress.”
NIST has identified several PQC algorithms with the potential to become future security standards as practical quantum computers emerge, with the U.S. federal government targeting a transition by 2035. However, Moody warns that organizations should act promptly. “These studies reinforce that the window for migration is limited, making immediate action imperative,” he concludes.
Topics:
- Safety/
- Quantum Computing
Source: www.newscientist.com